Introducing EP Audit

Photo by Bimal Gharti Magar, 2026.
In the complex landscape of cloud security, staying compliant and prepared for audits is important. Enter EP Audit, a compliance-focused audit process, AI-powered but led by senior engineers. It’s designed for Azure, AWS, and Google Cloud setups. EP Audit emerged from necessity: When a financial services client required an Azure security audit, we at End Point built a solution that not only met their immediate needs, but also evolved into an internal tool we continue to refine. Today, it serves as a key part of our multi-cloud security audit framework and is tested against our own cloud accounts before being used in client engagements.
The Problem
Cloud environments are dynamic: New projects, personnel changes, and vendor updates can significantly alter configurations over time. As environments evolve, the security posture originally reviewed and approved by your engineers may no longer fully match what is running in production. Unused resources, overly permissive access, and orphaned infrastructure can also accumulate over time, increasing both risk and monthly costs. This often goes unnoticed until an audit, customer review, or security incident forces a closer look.
Modern compliance frameworks—SOC 2, ISO 27001, HIPAA, PCI DSS—require regular, documented security reviews. Yet many organizations still struggle to provide consistent documentation with timestamps, severity tracking, and proof of remediation. EP Audit helps address this gap by generating a structured audit trail throughout the review process.
What EP Audit Looks Like
An EP Audit engagement is structured as a scheduled review cycle with two phases: a Base scan to establish a security snapshot, and a Final scan performed after remediation work to verify fixes. Both phases use a command-line runner with a read-only audit identity, ensuring no changes are made during the audit itself. Each Base scan produces nine deliverables designed to provide both high-level summaries and detailed technical findings:
- Executive Summary: Severity-ranked audit findings.
- Client Report: Full narrative with risk scorecard and roadmap.
- Structured Findings Report: Engineer-friendly findings by category.
- Pre-filled Hardening Checklist: CIS-aligned checklist with auto-populated FAIL statuses.
- Fillable Hardening Checklist: A remediation tool for your team.
- Network Diagram: Auto-generated deployment topology.
- Findings Workbook: Excel file with color-coded severity tabs.
- Remediation Plan: Phased plan with affected resources.
- Partner Remediation Identity Setup: Guide for temporary write scope during remediation.
These deliverables are standardized across Azure, AWS, and GCP, helping simplify multi-cloud audit reviews and recurring engagements.
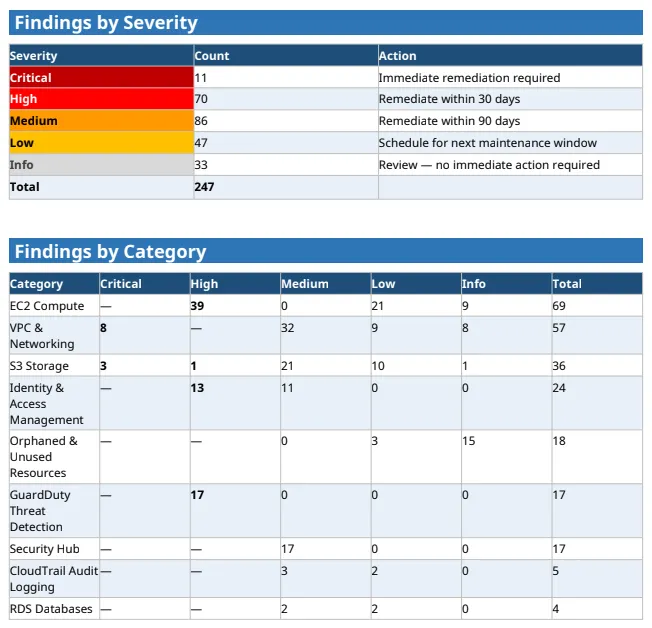
Sample summary of findings by severity and category on EP Audit.
Every finding in EP Audit is mapped to controls from recognized security frameworks. For Azure, we reference the CIS Microsoft Azure Foundations Benchmark and the Microsoft Cloud Security Benchmark. AWS findings align with the CIS AWS Foundations Benchmark, AWS Foundational Security Best Practices, and related guidance. GCP findings follow the CIS GCP Foundation Benchmark and the Google Cloud Architecture Framework Security Pillar. This helps keep audit findings grounded in established industry standards rather than proprietary scoring systems or arbitrary recommendations.
A Service, Not Just a Tool
There are already plenty of cloud configuration scanners available. What matters is how the findings are reviewed, prioritized, and applied in real environments.
- Senior Engineering Review: Our engineers provide context and actionable recommendations for each finding, bridging the gap between automated results and practical solutions.
- End Point-Specific Enhancements: We include checks beyond published frameworks, such as billing data analysis for orphaned resources and third-party security tool integration.
- Internal Validation: Every framework change is tested on End Point’s own cloud accounts before client deployment.
A single audit provides a snapshot in time, but recurring audits make it easier to identify trends, validate remediation progress, and detect configuration drift over time. EP Audit includes year-over-year comparison reporting to help highlight both improvements and regressions. In practice, this helps support compliance reviews, procurement questionnaires, and ongoing security review processes while providing better visibility into how environments evolve over time.
Phased Remediation
EP Audit generates remediation scripts and recommendations organized by severity:
- P1 (0–7 days): Critical issues like exposed management ports.
- P2 (30 days): High-priority issues such as encryption gaps.
- P3 (90 days): Medium-priority defense-in-depth weaknesses.
- P4 (Maintenance): Low-priority configuration hygiene.
Scripts default to dry-run mode, allowing proposed changes to be reviewed before execution. Our team can assist with remediation directly, or clients can implement the recommendations independently using the provided guidance.
Over multiple engagements, organizations begin building a clearer picture of how their cloud environments evolve over time. Recurring audits make it easier to track remediation progress, identify recurring issues, and detect configuration drift before it becomes a larger problem. The resulting documentation can also help support compliance reviews, customer security questionnaires, cyber insurance requirements, internal security tracking, and reduce monthly costs.
Working with End Point
If your organization operates workloads in Azure, AWS, or Google Cloud and needs a structured, standards-aligned cloud security review process, feel free to contact us. If you are working with us already, you can talk with your representative to find out more.
Comments